Guide to Retrieve the Secret Value Using AWS Secret Manager

App developers are hunting all possible means to find a secure way to store their data in the database or Redis. (Redis is an open-source in-memory Data Structure Store, used as a database and a caching layer or a message broker.) One of the challenging tasks with the database is the storage and retrieval, the process is hard to code. And AWS Secret Manager is a problem solver. The AWS Secret Manager focuses to keep your data in secret. The secrets may be your database credentials, passwords or third party API.
Let us walk you through the process of how to keep the Secret a secret using the AWS Secret Manager.
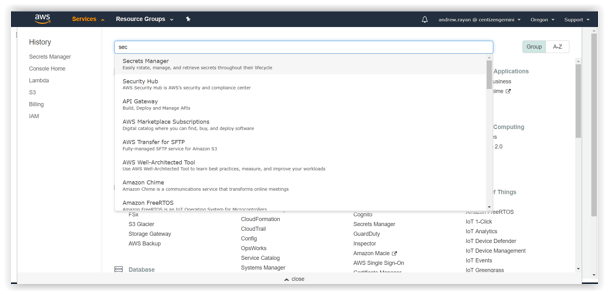
1.Log into your AWS account, search and select the Secret Manager. Afterwards, enter into the Secret Manager Console and click on the “Store a new secret”.
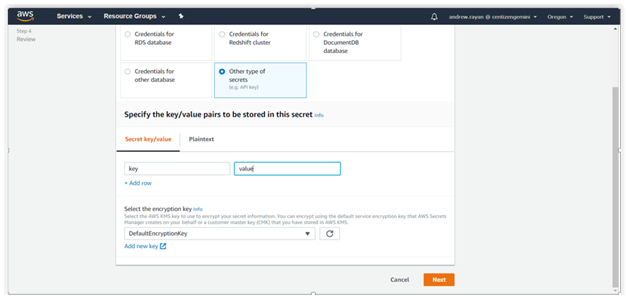
2. In the “Store a new secret” option, you will find the options to select a Secret type.
- Credentials for RDS database
- Credentials for Redshift Cluster
- Credentials for Document database
- Credentials for Other database
- Other type of secrets
If you do not have a definite value, go with “Other type of secrets”. Then enter the appropriate key name and hit Next.
Specify the “Secret name and its description” in the particular fields and other options (optional). Just hit Next.
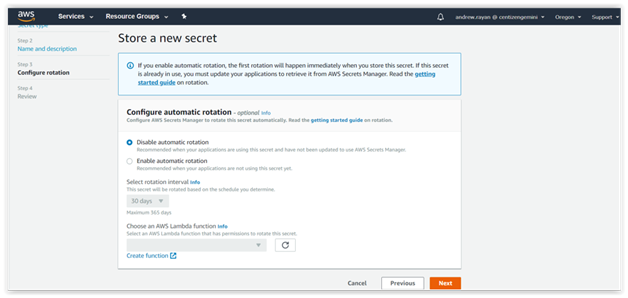
3. After completing Steps 1 and 2, you will be taken to the “Configure Automatic Rotation”. There is an available option to “Disable or Enable the automatic rotation” of the keys via lambda function. Select “Disable” and follow to the next level.
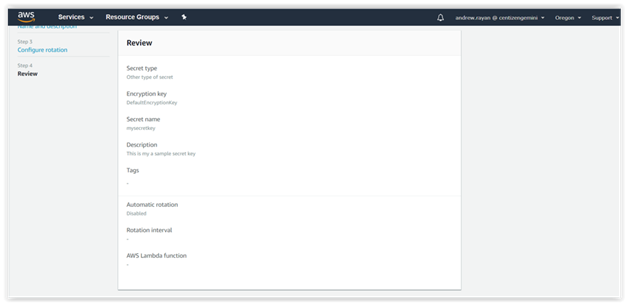
4. You can “Review”, your data in the previous steps and click “Store” button. Then, you’ll get the sample snippets of Java.
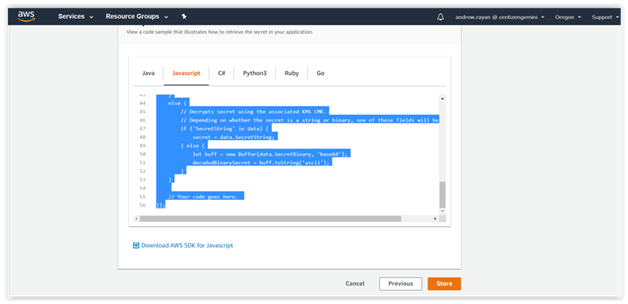
This is the generated Snippet code sample:</.h2
// Use this code snippet in your app.
// If you need more information about configurations or implementing the sample code, visit the AWS docs:
// https://aws.amazon.com/developers/getting-started/nodejs/
// Load the AWS SDK
var AWS = require(‘aws-sdk’),
region = “us-west-2”,
secretName = “mysecretkey”,
secret,
decodedBinarySecret;
// Create a Secrets Manager client
var client = new AWS.SecretsManager({
region: region
});
// In this sample we only handle the specific exceptions for the ‘GetSecretValue’ API.
// See https://docs.aws.amazon.com/secretsmanager/latest/apireference/API_GetSecretValue.html
// We rethrow the exception by default.
client.getSecretValue({SecretId: secretName}, function(err, data) {
if (err) {
if (err.code === ‘DecryptionFailureException’)
// Secrets Manager can’t decrypt the protected secret text using the provided KMS key.
// Deal with the exception here, and/or rethrow at your discretion.
throw err;
else if (err.code === ‘InternalServiceErrorException’)
// An error occurred on the server side.
// Deal with the exception here, and/or rethrow at your discretion.
throw err;
else if (err.code === ‘InvalidParameterException’)
// You provided an invalid value for a parameter.
// Deal with the exception here, and/or rethrow at your discretion.
throw err;
else if (err.code === ‘InvalidRequestException’)
// You provided a parameter value that is not valid for the current state of the resource.
// Deal with the exception here, and/or rethrow at your discretion.
throw err;
else if (err.code === ‘ResourceNotFoundException’)
// We can’t find the resource that you asked for.
// Deal with the exception here, and/or rethrow at your discretion.
throw err;
}
else {
// Decrypts secret using the associated KMS CMK.
// Depending on whether the secret is a string or binary, one of these fields will be populated.
if (‘SecretString’ in data) {
secret = data.SecretString;
} else {
let buff = new Buffer(data.SecretBinary, ‘base64’);
decodedBinarySecret = buff.toString(‘ascii’);
}
}
// Your code goes here.
});
Hope this helped you learn a way to secure your content.
Centizen
A Leading IT Staffing, Custom Software and SaaS Product Development company founded in 2003. We offer a wide range of scalable, innovative IT Staffing and Software Development Solutions.
Contact Us
USA: +1 (971) 420-1700
Canada: +1 (971) 420-1700
India: +91 63807-80156
Email: contact@centizen.com
Our Services
Software Development
IT Staffing
General Staffing
Remote Hiring
Products
Software Development
UI/UX Design
Product Development
Devops Services
Managed Cloud Services
Tech Stack
Contact Us
USA: +1 (971) 420-1700
Canada: +1 (971) 420-1700
India: +91 63807-80156
Email: contact@centizen.com